Habilitación del escaneo para patrones no de proveedor
Puede habilitar la exploración de patrones no pertenecientes a proveedores. Los patrones que no son de proveedor corresponden a secretos como claves privadas.
Para obtener más información sobre patrones que no son de proveedor, consulta "Patrones de análisis de secretos admitidos".
-
En GitHub, navegue hasta la página principal del repositorio.
-
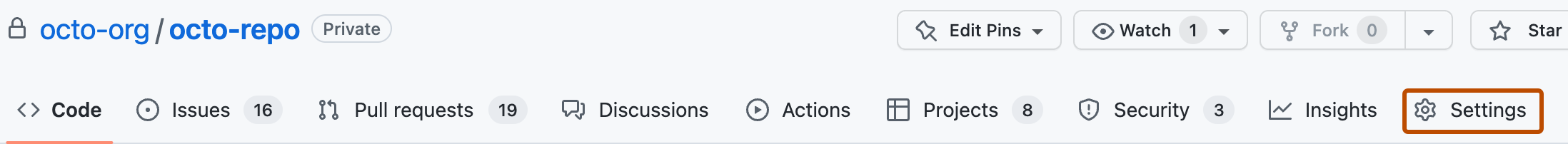
Debajo del nombre del repositorio, haz clic en Settings. Si no puedes ver la pestaña "Configuración", selecciona el menú desplegable y, a continuación, haz clic en Configuración.
-
En la sección "Security" de la barra lateral, haz clic en Advanced Security.
-
En "Secret Protection", a la derecha de "Patrones que no son de proveedor", haz clic en Habilitar.