Puede habilitar comprobaciones de validez de repositorios individuales a través de la configuración del repositorio. Las comprobaciones de validez comprueban si los secretos detectados siguen activos, lo que le ayuda a priorizar los esfuerzos de corrección. Para obtener información sobre qué son las comprobaciones de validez y cómo funcionan, consulte Acerca de las comprobaciones de validez.
Para obtener una lista de los patrones secretos que admiten comprobaciones de validez, consulte Patrones de análisis de secretos admitidos.
Habilitación de comprobaciones de validez
Para habilitar las comprobaciones de validez desde la interfaz de usuario:
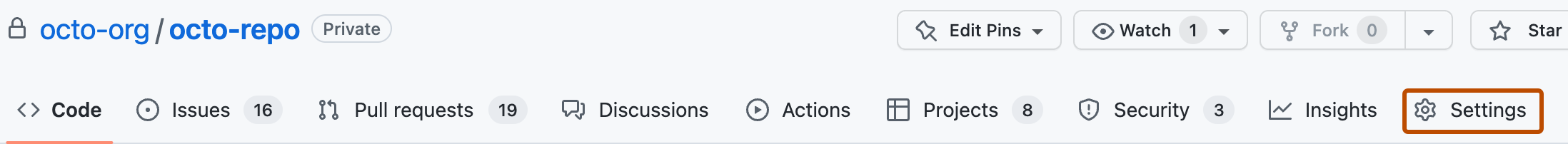
es-ES: 1. En GitHub, navegue hasta la página principal del repositorio.
-
Debajo del nombre del repositorio, haz clic en Settings. Si no puedes ver la pestaña "Configuración", selecciona el menú desplegable y, a continuación, haz clic en Configuración.
-
En la sección "Security" de la barra lateral, haz clic en Advanced Security. 1. En Secret scanning, selecciona la casilla situada junto a "Comprobar automáticamente si un secreto es válido mediante el envío al asociado correspondiente".
-
Desplácese hasta la parte inferior de la página y haga clic en Guardar cambios.
Nota:
También puedes usar la API de REST para habilitar las comprobaciones de validez de los patrones de asociados para tu repositorio. Para más información, consulta Puntos de conexión de la API de REST para repositorios.
Como alternativa, los propietarios de la organización y los administradores de empresa pueden habilitar la característica para todos los repositorios de la organización o empresa. Para obtener más información, vea Creación de una configuración de seguridad personalizada y Creación de una configuración de seguridad personalizada para su empresa.