Note
Extended metadata checks for tokens is in public preview and subject to change.
Note
Starting on February 18, 2026, GitHub will automatically enable extended metadata checks for repositories that have validity checks enabled. For repositories managed by security configurations, GitHub will update those configurations and apply the feature to attached repositories. This is a one-time transition to help organizations benefit from enhanced metadata without manual configuration.
This article shows how you can enable extended metadata checks for individual repositories through repository settings. Alternatively, you can enable them at scale using security configurations at the organization or enterprise level. See Creating a custom security configuration or Creating a custom security configuration for your enterprise.
Prerequisites
Before enabling metadata checks, you need to ensure that validity checks are enabled for the repository. See Enabling validity checks for your repository.
Enabling extended metadata checks
-
On GitHub, navigate to the main page of the repository.
-
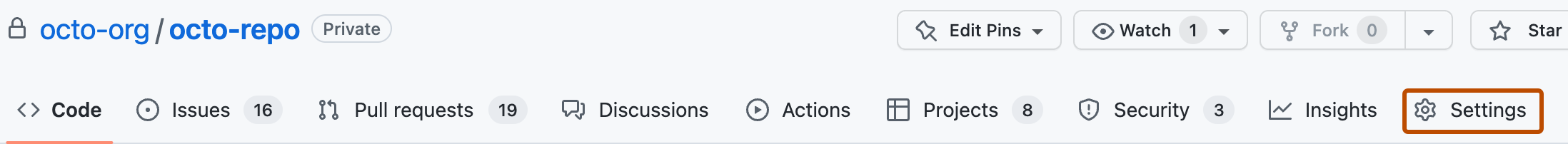
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then click Settings.
-
In the "Security" section of the sidebar, click Advanced Security.
-
Under "Secret Protection" and "Validity checks", to the right of "Extended metadata", click Enable.