Nota:
La omisión delegada para la protección de inserción se encuentra actualmente en beta y está sujeta a cambios.
La omisión delegada de la protección de inserción permite definir quién puede insertar confirmaciones que contienen secretos y agrega un proceso de aprobación para otros colaboradores. Consulta Acerca de la omisión delegada para la protección de inserción.
Para habilitar la omisión delegada, cree los equipos o roles que administrarán las solicitudes de omisión.
Habilitación de la omisión delegada para un repositorio
Nota:
Si un propietario de la organización o de la empresa configura el bypass delegado a nivel de organización o de empresa, las configuraciones a nivel de repositorio se deshabilitan.
-
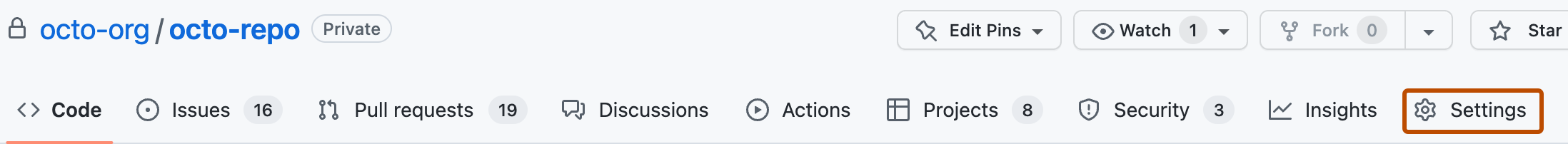
En GitHub, navegue hasta la página principal del repositorio.
-
Debajo del nombre del repositorio, haz clic en Settings. Si no puedes ver la pestaña "Configuración", selecciona el menú desplegable y, a continuación, haz clic en Configuración.
-
En la sección "Security" de la barra lateral, haz clic en Code security and analysis.
-
En "Code security and analysis", busca "GitHub Advanced Security."
-
En "Protección de inserción", a la derecha de "Quién puede omitir la protección de inserción para secret scanning", seleccione el menú desplegable y, a continuación, haga clic en Roles o equipos específicos.
-
En "Bypass list", haz clic en Add role or team.
-
En el cuadro de diálogo, seleccione los roles y equipos que desea agregar a la lista de omisión y haga clic en Agregar seleccionado.
Nota:
No se pueden agregar equipos secretos a la lista de omisión.
Habilitación de la omisión delegada para una organización
-
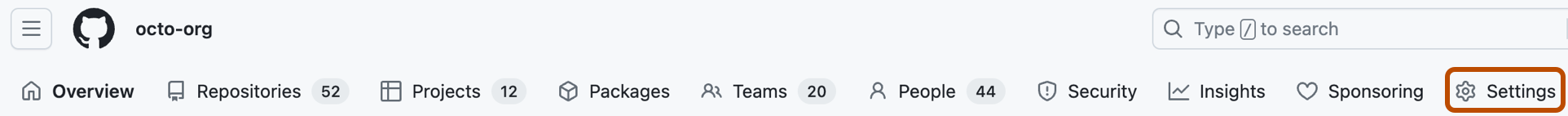
En GitHub, navega a la página principal de tu organización.
-
Debajo del nombre de la organización, haz clic en Settings. Si no puedes ver la pestaña "Configuración", selecciona el menú desplegable y, a continuación, haz clic en Configuración.
-
En la sección "Security" de la barra lateral, haz clic en Code security and analysis.
-
En "Code security and analysis", busca "GitHub Advanced Security."
-
En "Protección de inserción", a la derecha de "Quién puede omitir la protección de inserción para secret scanning", seleccione el menú desplegable y, a continuación, haga clic en Roles o equipos específicos.
-
En "Bypass list", haz clic en Add role or team.
-
En el cuadro de diálogo, seleccione los roles y equipos que desea agregar a la lista de omisión y haga clic en Agregar seleccionado.